K365 Edr refers to an advanced technological solution within the field of endpoint detection and response (EDR). It plays a pivotal role in modern cybersecurity frameworks, offering comprehensive threat detection, investigation, and response capabilities. This article delves into the intricate workings of K365 Edr, its benefits, implementation strategies, and key considerations for organizations looking to bolster their digital defenses.

In the rapidly evolving landscape of cybersecurity, K365 Edr has emerged as a formidable ally for organizations striving to safeguard their digital environments. This cutting-edge endpoint detection and response (EDR) platform is designed to empower security teams with the tools they need to identify and neutralize threats swiftly. As cyber threats become more sophisticated, the demand for robust solutions like K365 Edr continues to grow.
The digital domain is increasingly becoming a battleground where organizations fight to protect sensitive data against relentless cyber adversaries. K365 Edr provides significant advantages not only in detection and response but also in prevention and compliance, making it vital for all types of organizations—from small businesses to large enterprises. Understanding how K365 Edr works can help organizations striking a balance between comprehensive security measures and efficient resource management.
At its core, K365 Edr provides comprehensive visibility into endpoint activities, enabling real-time monitoring and analysis. By leveraging advanced analytics and machine learning, it identifies abnormal behaviors and potential threats. This proactive approach ensures that even the very elusive threats are detected before they can inflict damage. The platform integrates seamlessly into existing IT infrastructures, offering a user-friendly interface that simplifies complex security operations.
Additionally, the platform is designed to gather telemetry data from various endpoints, which means it can continuously monitor traffic patterns, file accesses, and user behaviors, leveraging this insight for enhanced detection capabilities. This feature is crucial in today’s cybersecurity landscape, where threats can pivot and evolve rapidly. K365 Edr does not just react to threats; its AI-driven analytics provide predictive capabilities, helping organizations anticipate potential breach scenarios before they materialize.
Moreover, K365 Edr enables context-rich alerts, reducing false positives and ensuring that security teams focus on genuine threats rather than getting bogged down by inconsequential alerts. The richness of data and analytics that K365 Edr provides plays a critical role in supporting investigations, allowing security teams to assess and understand incidents better, thereby improving their response strategies.
The adoption of K365 Edr yields numerous benefits for organizations committed to enhancing their security posture. Firstly, its real-time threat detection capabilities allow for immediate incident response, reducing potential downtime and data loss. With continuous monitoring capabilities, organizations can maintain an understanding of their security posture in real-time, ensuring that threats are identified and dealt with without delay.
Moreover, the ability to investigate and analyze threat vectors in detail aids in comprehensive post-incident analysis, facilitating continuous improvement of security measures. This built-in review mechanism allows organizations to learn from past incidents, making the system smarter and more resilient over time. Organizations can utilize insights gathered from K365 Edr to inform future security policies, ultimately leading them to respond more effectively to the evolving threat landscape.
Additionally, K365 Edr's automated response mechanisms relieve the burden on human resources, enabling security teams to focus on strategic initiatives rather than routine tasks. This efficiency not only enhances operational productivity but also strengthens the organization's overall resilience against cyber threats. For instance, by automating tasks such as isolating infected endpoints or deploying patches, K365 Edr helps organizations swiftly mitigate risks without manual intervention, allowing IT personnel to redirect their focus on more strategic areas such as security architecture and policy formulation.
The efficiency of K365 Edr extends beyond just automation; its comprehensive reporting tools provide leadership with insights into the efficacy of their security strategies. Such transparency is invaluable for compliance purposes and board-level discussions, where stakeholders are increasingly interested in risk management and the organization’s overall security posture. Organizations can better allocate budgets and resources by clearly understanding threat landscapes and risk profiles.
Finally, implementing K365 Edr not only fulfills an immediate security need but can also significantly contribute to the long-term digital transformation goals of an organization. By fostering a culture of security within an organization, K365 Edr contributes to creating accountable practices and awareness, ultimately leading to a more security-conscious workforce.
For organizations contemplating the integration of K365 Edr, several critical factors must be considered. Firstly, understanding the existing security infrastructure is pivotal to ensure seamless integration. Organizations should assess their current capabilities and identify potential gaps that K365 Edr can fill. This evaluation helps in tailoring the deployment to address specific security needs.
Another essential consideration is the need for comprehensive training for IT staff. As K365 Edr introduces new functionalities, equipping the security team with the necessary skills is vital for optimal usage. Ongoing training sessions and workshops ensure that the team remains updated on the latest features and threat intelligence. The importance of this ongoing education cannot be overstated, as cyber threats constantly evolve, and keeping the team abreast of the latest tactics used by attackers is critical for maintaining a robust defense.
Further, organizations must evaluate their incident response capabilities in concert with deploying K365 Edr. A well-defined incident response plan that integrates K365 Edr's capabilities can dramatically enhance the effectiveness of the platform itself. The response plan should account for various scenarios, identifying roles, and responsibilities among the team and ensuring that all members know how to use the technology to its fullest potential during a breach situation.
Another consideration is the scalability of K365 Edr. As organizations grow, so do their cybersecurity needs. Ensuring that the EDR solution can effectively scale alongside the organization is crucial for sustaining long-term security efforts. Organizations should seek clarity on how the platform can adapt to increasing workloads and evolving infrastructure and whether additional features or licenses might be necessary down the line.
Finally, compliance considerations should also be top of mind. Organizations juggling various regulatory obligations might discover that K365 Edr offers features that assist in complying with those requirements. However, understanding how to align the tool’s capabilities with external regulations is an integral part of the deployment strategy. Engagement with legal or compliance professionals can provide added assurance that the deployment of K365 Edr will contribute positively to the organization’s compliance posture.
Effective implementation of K365 Edr requires a strategic approach. Organizations can start with a phased deployment, which involves adopting the solution in stages. This approach allows for controlled testing and adjustment, minimizing disruptions to existing systems. Pilot testing on a subset of endpoints provides valuable insights into performance and paves the way for full-scale implementation.
Collaboration with experienced vendors and consultants is also beneficial during the implementation phase. Their expertise ensures that the deployment aligns with industry top practices and adheres to regulatory standards, thereby enhancing overall security outcomes. Engaging experts helps organizations avoid common pitfalls in deployment, as they can provide insights based on real-world experience with diverse environments and threats.
Additionally, organizations should involve various stakeholders in the implementation process. Security, IT operations, compliance, and risk management personnel should work together to ensure that K365 Edr is not only well configured but also aligned with the organization's broader objectives. This collaboration creates a more holistic security approach, as insights from different departments can lead to more robust security policies and practices.
Post-implementation, organizations should establish a feedback mechanism to continuously assess the performance of K365 Edr. Collecting feedback from users will help identify any challenges or areas that need improvement. Regular reviews of the deployed solution can also provide valuable insights into how it can be optimized for greater effectiveness. This practice of continuous improvement and adaptation should be ingrained in the organizational culture, enabling businesses to stay ahead of potential threats.
Lastly, organizations must maintain a clear communication strategy as part of the implementation and ongoing operation of K365 Edr. Keeping all stakeholders informed—ranging from IT teams to executive leadership—ensures that the organization remains committed to cybersecurity as a shared priority. This strategy reinforces the need for shared responsibility and accountability across the business, creating a united front against cyber threats.
| Aspect | Consideration |
|---|---|
| Integration | Seamless with existing infrastructure, ensuring minimal disruption. |
| Training | Ongoing staff education recommended to adapt to new features and threat intelligence. |
| Deployment | A phased approach is advisable, allowing tailored alignment with operational needs. |
| Expert Collaboration | Work with experienced vendors for best practices and compliance alignment. |
| Incident Response | Integrate K365 Edr into a well-defined incident response plan ensuring swift action and accountability. |
| Scalability | Ensure that the EDR solution can scale with business growth and evolving security needs. |
| Feedback Mechanism | Establish regular reviews and feedback channels post-implementation for continual optimization. |
In conclusion, K365 Edr stands as a crucial component in modern cybersecurity strategies. Its comprehensive capabilities, ranging from real-time threat detection to automated responses, offer organizations a robust defense mechanism against the ever-evolving landscape of cyber threats. By understanding the functionality, benefits, and implementation strategies of K365 Edr, organizations can bolster their security measures and safeguard their digital assets effectively. Additionally, ensuring that K365 Edr is woven into the fabric of the organization’s security culture will ultimately lead to more sustainable cybersecurity practices, aligning the technical aspects with human factors to create a more resilient and proactive approach to digital security.
Explore the Tranquil Bliss of Idyllic Rural Retreats

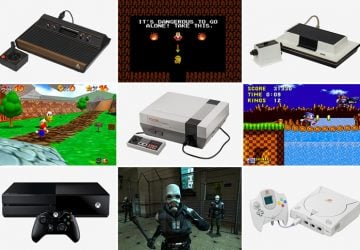
Ultimate Countdown: The 20 Very Legendary Gaming Consoles Ever!
Understanding Halpin and its Influence

Affordable Full Mouth Dental Implants Near You

Discovering Springdale Estates

Illinois Dentatrust: Comprehensive Overview

Embark on Effortless Adventures: Unveiling the Top in Adventures Made Easy Outdoor Equipment

Unveiling Ossur Valves: Innovation in Prosthetics

Unlock the Full Potential of Your RAM 1500: Master the Art of Efficient Towing!
