This article delves into the analysis of data strings like 3222d2656 within software systems, highlighting the importance of precise data management and processing in technological advancements. Understanding such data intricacies is crucial for software engineers seeking to improve system efficiency and accuracy. Techniques for managing and interpreting these data elements are discussed extensively, providing practical insights into optimizing digital processes.

In the intricately interconnected world of modern software systems, the role of data strings, such as "3222d2656", is pivotal. Data strings serve as fundamental units of measurement, providing critical information that can dictate how software functions, communicates, and evolves. They are not merely sequences of characters; they can be identifiers, keys, or tokens that represent various types of data based on the context in which they are used. This context is vital, as it lends meaning to the string and determines its significance within a given application.
The unique data string "3222d2656" might initially appear as a random sequence of characters. However, within its structure, it likely encodes specific information relevant to its application, possibly related to user identification, transactional processes, or system commands. Understanding and decoding such strings is essential for software developers who aim to streamline functionality and ensure data integrity across systems. The string could represent anything from a unique identifier for a user session to a hash of a password or even a database record identifier. Each context gives the string a different role, emphasizing the importance of understanding its intended use.
Deconstructing a data string involves several techniques which can vary depending on the complexity and the specific software context. These processes often include:
One of the main challenges in handling such data strings is ensuring the security and privacy of sensitive information. Developers must meticulously design systems that can both protect and efficiently process these strings. The potential for misuse or manipulation of data strings underscores the necessity for robust validation and sanitation processes to prevent security vulnerabilities such as SQL injection or data breaches.
For developers aspiring to gain proficiency in data string manipulation, here is a detailed step-by-step guide:
| Technology | Features | Applications |
|---|---|---|
| Python | Dynamic typing, extensive libraries, strong community support | Web development, data science, scripting, automation |
| Java | Object-oriented, high performance, rich ecosystem | Enterprise applications, mobile apps, large systems |
| JavaScript | Lightweight, versatile, essential for front-end development | Web development, server-side programming with Node.js |
What is a data string in software systems?
A data string is a sequence of characters representing specific information used by software applications to perform various functions. These can include identifiers, keys, or data payloads, with each string typically designed for a particular purpose depending on the application context.
Why is it important to analyze data strings like 3222d2656?
Analyzing data strings helps in debugging, optimizing code, ensuring data security, and improving overall system functionality. Understanding these strings allows developers to track interactions, analyze user behavior, and ensure that data integrity is maintained throughout various operations.
What are common tools for handling data strings?
Mature programming languages like Python, Java, and JavaScript are often used due to their robust libraries and frameworks supporting data manipulation. Tools such as regular expressions for string patterns, serialization libraries for data encoding, and debugging tools for performance monitoring also play a significant role in processing data strings.
Are there any security concerns with data strings?
Yes, particularly regarding data integrity and privacy. It's essential to adopt encryption and secure data handling practices to safeguard information. This means implementing secure protocols, validating user input to prevent injection attacks, and storing sensitive data in encrypted formats to minimize the risk of data breaches.
In evaluating and processing data strings such as "3222d2656," the expertise of software engineers is imperative. Their ability to decode, interpret, and apply such data effectively shapes the efficiency, security, and advancement of contemporary technology solutions.
While the foundational techniques for handling data strings are essential, advanced methods significantly enhance capabilities in software development. These methods may involve leveraging sophisticated algorithms and frameworks tailored to specific tasks. Here are some advanced techniques worth exploring:
Regular expressions are a powerful tool for string manipulation, allowing developers to search, match, and modify strings effectively. Regular expressions can be used to validate formats (e.g., email addresses, phone numbers) and extract specific parts of strings with precision. Creating complex patterns can significantly reduce the amount of code required to perform string operations and enhance overall performance.
String interpolation is a method where variables can be inserted into string literals, making code cleaner and easier to read. Languages like Python utilize f-strings, and JavaScript has template literals for a similar effect. Proper string formatting can reduce bugs by making the code more understandable and can also improve performance when constructing complex strings.
Understanding the difference between immutable and mutable strings is crucial, especially in languages like Java, where strings are immutable. Methods like StringBuilder (in Java) or StringBuffer allow for efficient string manipulations without creating new objects, which is essential for performance-sensitive applications. In Python, while strings are immutable, using lists to build strings can enhance efficiency before joining them into a final result.
Data compression techniques, such as gzip or Brotli, can significantly reduce the size of the data strings, particularly when transmitting data over networks. Moreover, encoding formats like Base64 are common when working with binary data in text-only environments. Understanding when and how to apply these techniques can lead to substantial improvements in data handling.
In software applications that process data strings, robust error handling is vital. Proper validation checks before processing inputs can prevent runtime errors and enhance the user experience. Additionally, providing clear feedback on errors can guide users in correcting their input, thereby improving overall application usability.
Looking towards the future, the role of data strings in software development is likely to become even more critical. As applications become increasingly complex and interconnected, the need for efficient data manipulation will grow. Here are some trends that may shape the future:
Machine learning algorithms increasingly rely on data strings for training models and making predictions. Data preprocessing, which often involves the manipulation of strings, will become an essential skill for developers working in this space. Techniques to convert text data into structured formats (like TF-IDF for textual data) will foster better model accuracy.
The rise of NLP applications means handling abundant data strings that represent human language. Developers will need to harness complex string techniques to extract meaning, sentiment, and context from vast textual data efficiently. This also correlates with the growing emphasis on building applications that can understand and generate human-like text.
In modern applications, real-time data processing has become paramount. Data strings are often used in real-time applications, from user interactions to IoT sensors. The strategies for handling incoming data strings promptly without loss or degradation of information become crucial for maintaining system integrity and user experience.
As data breaches become more common, there will be an increasing emphasis on securing data strings. Developers must anticipate threats and incorporate security best practices from the ground up, including end-to-end encryption and secure data transport protocols.
As software development evolves, coding standards regarding data string manipulation will likely become more refined. Best practices will focus on writing clean, maintainable code that handles strings efficiently, considering readability and collaboration among diverse development teams.
In conclusion, data strings, such as "3222d2656", are more than just random sequences; they represent critical elements within modern software architecture. By mastering techniques for string manipulation—from basic decoding to employing advanced algorithms—developers can unlock the full potential of their applications.
The future of software will undoubtedly involve even greater dependence on these essential components, and staying abreast of best practices will be key. As technology continues to evolve, the art of managing data strings will remain a cornerstone of effective software engineering, allowing developers to build secure, efficient, and user-friendly applications.
Explore the Tranquil Bliss of Idyllic Rural Retreats

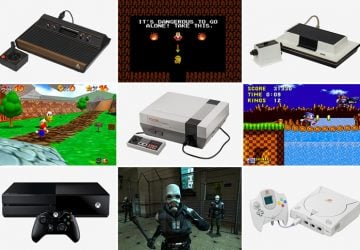
Ultimate Countdown: The 20 Very Legendary Gaming Consoles Ever!
Understanding Halpin and its Influence

Affordable Full Mouth Dental Implants Near You

Discovering Springdale Estates

Illinois Dentatrust: Comprehensive Overview

Embark on Effortless Adventures: Unveiling the Top in Adventures Made Easy Outdoor Equipment

Unveiling Ossur Valves: Innovation in Prosthetics

Unlock the Full Potential of Your RAM 1500: Master the Art of Efficient Towing!
